The Australian Cyber Security Centre (ACSC) has released their latest threat report which covers cyber incidents reported from July 2019 to June 2020. The ACSC is a government agency that researches cybersecurity and provides cyber education to government, organizations and individuals based on their research and best practices about cyber awareness and protection.
This report examined the number of incidents per industry sector, as well as the types of cyber incidents that were reported to the ACSC.
Threat analysis according to the ACSC report
Industry sector incidents from 2019 to 2020
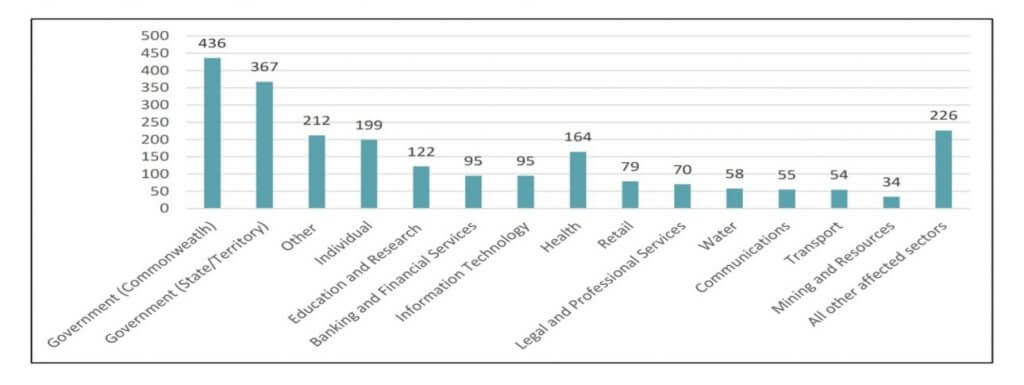
The graph above displays the results obtained by the ACSC, which shows the highest incident reported was by the public sector.
The chart below showcases the type of threats and the cybercrimes committed.

The most common threat type reported this year was malicious emails, followed by compromised systems, then scanning/reconnaissance/brute force attacks.
Implications for business
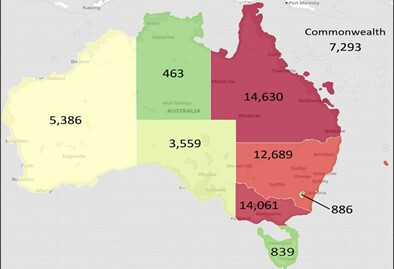
The map above showcases the number of cybercrimes per state in Australia, with Queensland having the most cybercrimes reported, followed by Victoria then New South Wales.
As we become more inter-connected and businesses undergo digital transformations, the playing field for cyber criminals expands as they continue to come up with new and innovative methods of breaking/exploiting systems. Not to mention that between system, process and humans, the weakest link in the trio is the human factor. This is supported by the fact that malicious emails are the most used exploit for cybercrime here in Australia.
In order to prevent such threats and exploitation, we all have a role to play as part of being a digital citizen. Extra caution must be taken when using systems, and security strategies and frameworks should be implemented and followed for businesses and governmental bodies. Individuals and employees should undertake training to develop best cyber hygiene practices and awareness.
If your business requires security consulting or a cyber strategy developed, please contact us at Agilient for assistance.
Author: Saeed Baayoun, Agilient Consultant
